How to use authentication?
There are two methods to access protected data in the dataset: Bearer Token Login and OAuth2 authentication. Both authentication methods can be used within a browser or from the command line, with only slight differences.
Hint
The Open Data provided by the Open Data Hub can be freely accessed, authentication is meant only for internal use.
In this section we show how to use authentication within the Open Data Hub, provided that you own an username and a password to access the closed data in the datasets.
To obtain the credentials, please send an email to . This action will open a support ticket that will be taken in charge by the Customer Support Team.
Bearer Token Login
Bearer token login is used to access the Datasets; description of the procedure is available at Authentication with Swagger.
OAuth2 authentication
OAuth2 authentication can be used in all the Datasets
that are marked with the  badge, so pick one dataset and go to
its swagger interface, whose URL is provided together with the
information of the dataset.
badge, so pick one dataset and go to
its swagger interface, whose URL is provided together with the
information of the dataset.
Note
As of Sep 29, 2023, authentication is not yet publicly available, so the following guidelines can not yet be put in practice.
If you use a browser
Make sure you have obtained a valid username and password, then open the /rest/refresh-token method and write you username and password in the two user and pw fields, respectively, as shown in Figure 31.
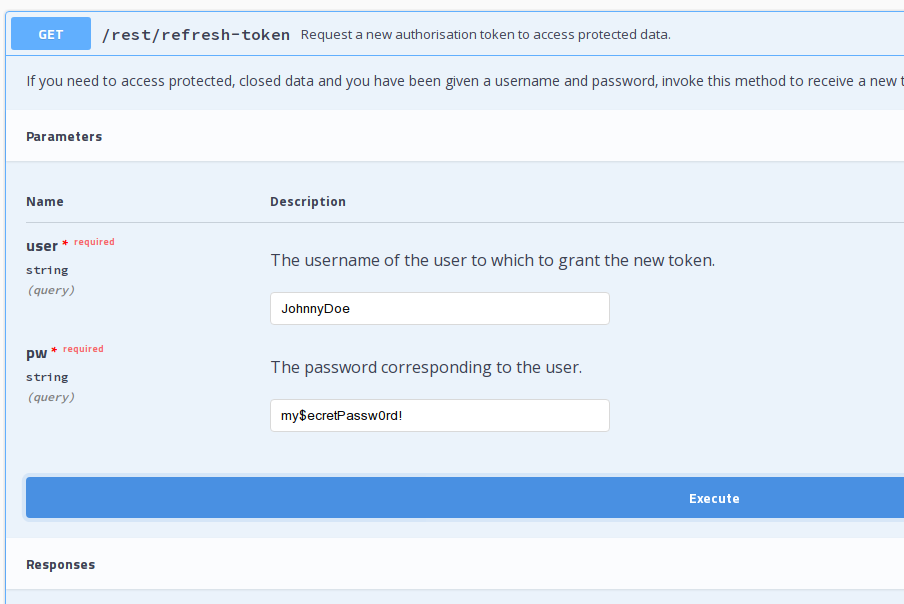
Figure 31 Request a new OAuth2 token.
If your credentials are valid, you will receive a new token, otherwise the response will be a 401 Unauthorized error message.
The token you received can be used in any of the API’s methods that
require authorisation. A sample call is shown in figure
Figure 32. Note the syntax of the Autorization
parameter: You must use prefix the authentication token with the
Bearer string, followed by an empty space, then by the
token.
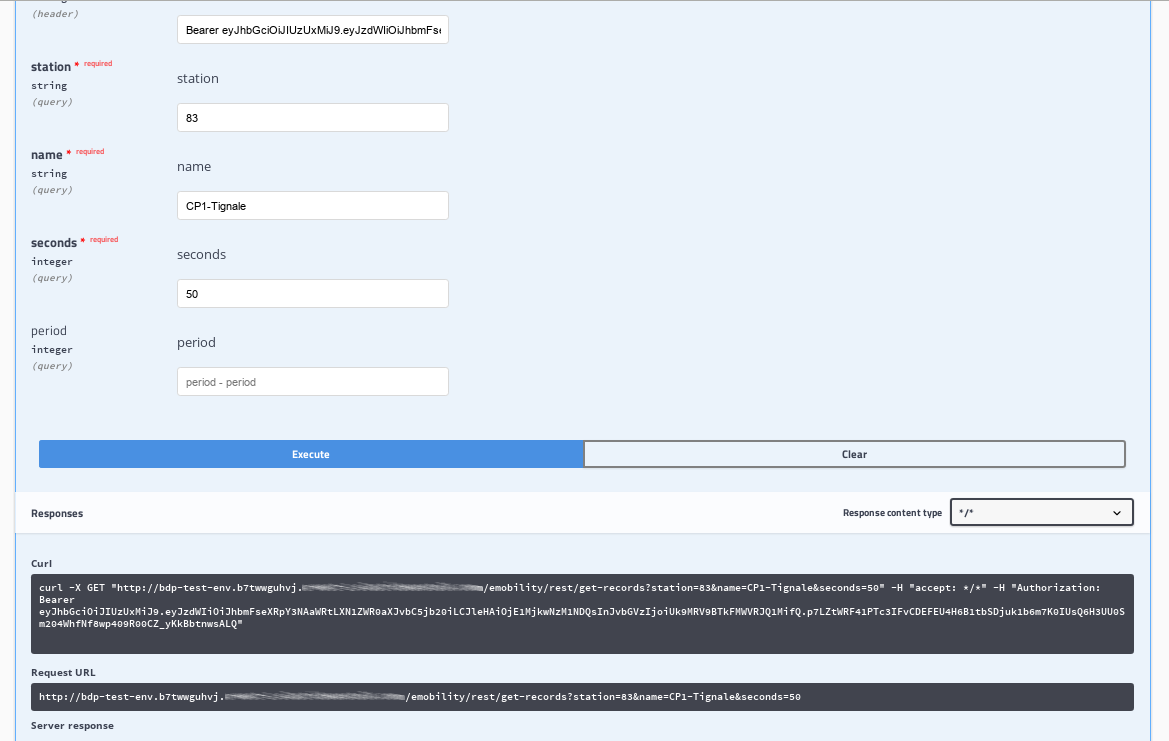
Figure 32 A successful call to a method requiring authentication.
In case you do not respect the Authorization+space+token sequence, use additional separators in the sequence (like Figure 33 shows), or use an invalid token, you will receive an 401 - Unauthorized HTTP response.
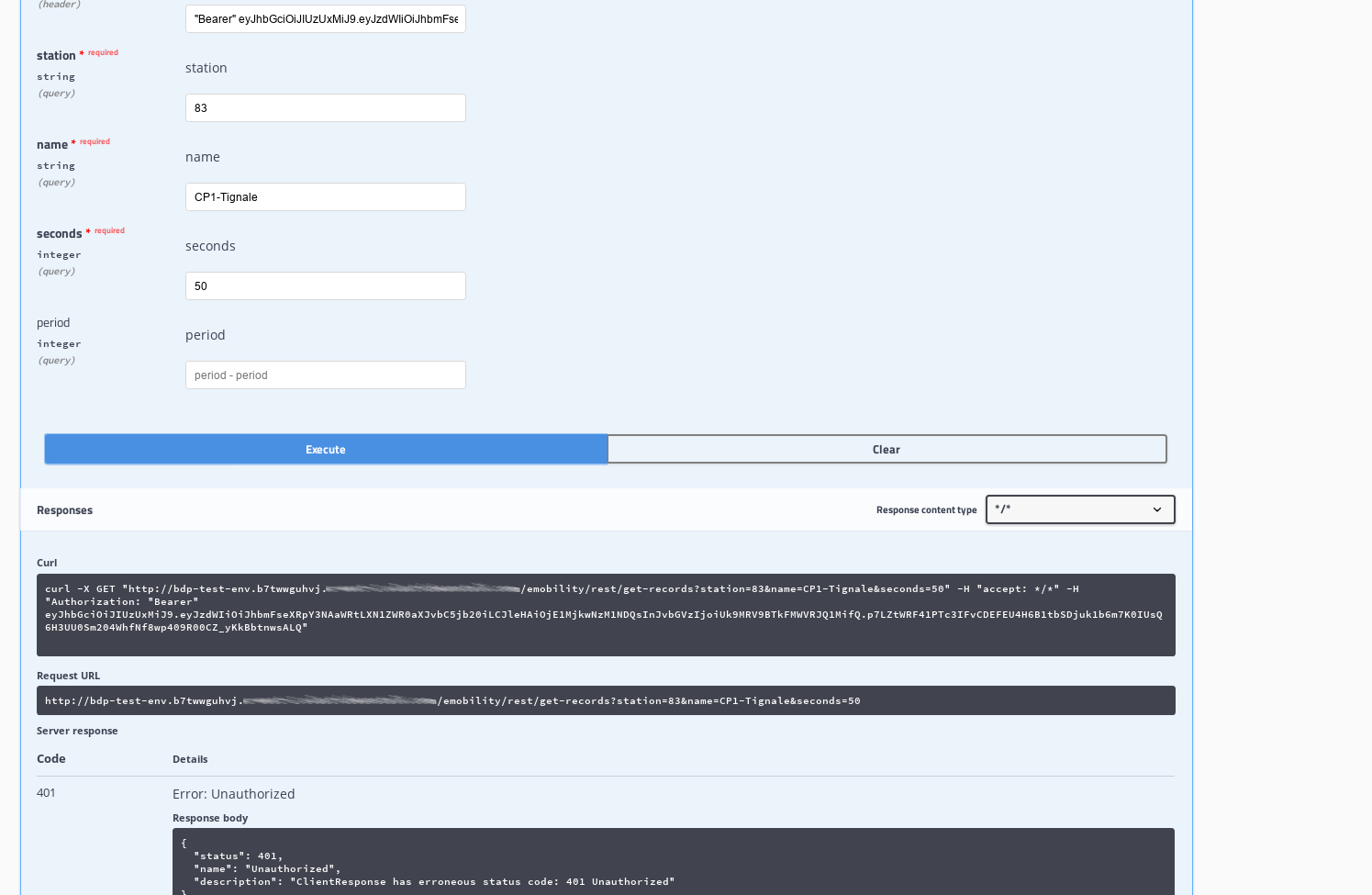
Figure 33 A failed call to a method requiring authentication.
If you use the Command Line Interface.
Open a shell on your workstation and use a tool like curl or wget, with the appropriate options:
-
-X Specify the request method (GET)
-
--header,-H Add extra header information to be included in the request.
Note that the --header option is used twice: The first to
receive the answer in text/html format, the second to
provide the credentials required to access protected content.
API calls can be done using a tool like curl or
wget, with the same -X and --header
option used twice: The first to require the format of the response,
the second to provide the credentials, like for example:
~$ curl -X GET "https://bdp-test-env.b7twwguhyj.example.com/emobility/rest/get-records?station=83&name=CP1-Tignale&seconds=50" --header "Accept: */*" --header 'Authorization: Bearer <token>'
Make sure to replace the <token> with the actual token you received.